Cybersecurity firm Kaspersky Labs revealed that the ASUS Live Update tool was compromised and used to install a malicious backdoor on ASUS devices. A file containing the malware with the malicious code was signed with legitimate ASUS digital certificates that made the Live Update tool think that the patch was authentic. Kaspersky estimated that around 500,000 devices downloaded the malicious update through ASUS’ live update tool but only about 600 systems were targeted. Symantec confirmed Kaspersky’s findings as around 13,000 computers using Symantec’s anti-virus were affected.
What is ASUS Live Update?
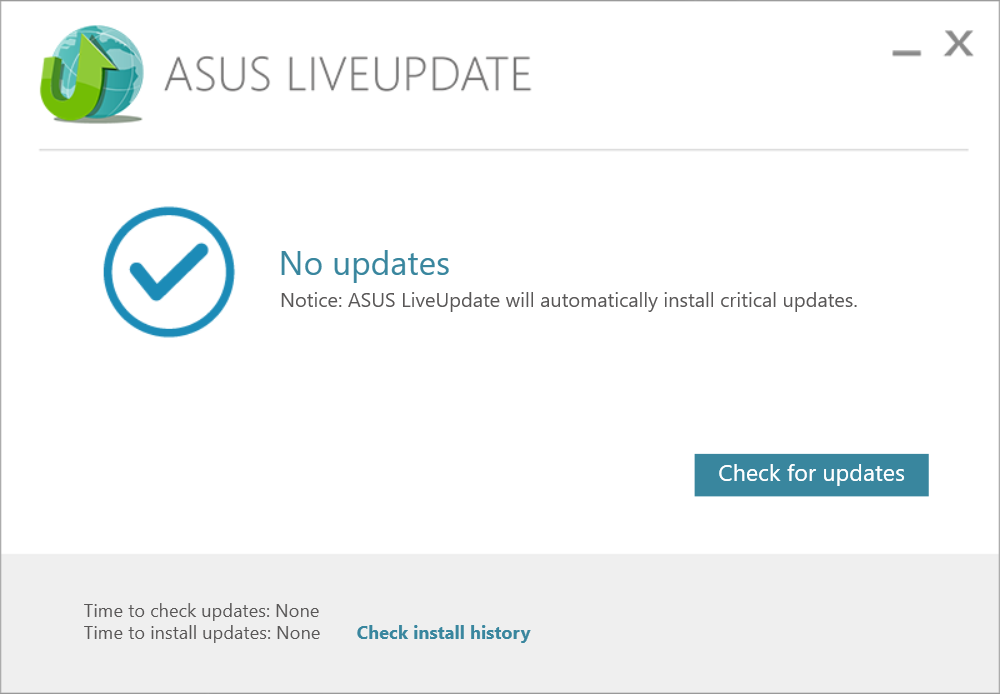
ASUS Live Update is a pre-installed software on most ASUS or ROG Laptops which handles the device’s updates outside Windows’ software updates. The Software covers driver updates and firmware updates for ASUS notebook computers.
Who are primarily affected?
The ASUS Live Update software is only for ASUS notebooks meaning users who have ASUS or ROG motherboards, Graphics Cards are not affected by the attack. Moreover, not all ASUS notebooks are affected even if they have the Live Update installed because it would require the Live Update software to run for it to download the malicious patch. So, there is a higher chance that you’re not affected if you don’t use the live update software anyway.
How do I know if my Laptop is breached?
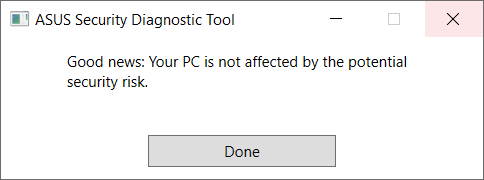
Once Kaspersky Lab announced the breach, ASUS released an official statement regarding the Live Update issue. Along with the official statement is a security diagnostic tool made by ASUS to determine if a laptop has been affected or not. Moreover, ASUS encourages its users to patch their Live Update software to version 3.6.8 as the latest update now has multiple security verification mechanisms to prevent similar forms of attack in the future.
SHOULD YOU BE WORRIED?
Attacks like these are no joke considering the tool was exploited since January and only has been discovered and fixed days before March ends. To Asus’ credit, the recent attack isn’t an exploit on a hardware level like Intel’s Spectre and Spoiler fiasco. And it’s definitely not as disastrous as facebook storing user’s password in plain text. Luckily enough the malware came from Advanced Persistent Threat(APT) groups that specifically target certain organizations or individuals instead of the general public.
Here’s the Official Statement by ASUS regarding the Hack:
Advanced Persistent Threat (APT) attacks are national-level attacks usually initiated by a couple of specific countries, targeting certain international organizations or entities instead of consumers.
https://www.asus.com/News/hqfgVUyZ6uyAyJe1
ASUS Live Update is a proprietary tool supplied with ASUS notebook computers to ensure that the system always benefits from the latest drivers and firmware from ASUS. A small number of devices have been implanted with malicious code through a sophisticated attack on our Live Update servers in an attempt to target a very small and specific user group. ASUS customer service has been reaching out to affected users and providing assistance to ensure that the security risks are removed.
ASUS has also implemented a fix in the latest version (ver. 3.6.8) of the Live Update software, introduced multiple security verification mechanisms to prevent any malicious manipulation in the form of software updates or other means, and implemented an enhanced end-to-end encryption mechanism. At the same time, we have also updated and strengthened our server-to-end-user software architecture to prevent similar attacks from happening in the future.
Additionally, we have created an online security diagnostic tool to check for affected systems, and we encourage users who are still concerned to run it as a precaution. The tool can be found here: https://dlcdnets.asus.com/pub/ASUS/nb/Apps_for_Win10/ASUSDiagnosticTool/ASDT_v1.0.1.0.zip
Users who have any additional concerns are welcome to contact ASUS Customer Service.
More information about APT groups: https://www.fireeye.com/current-threats/apt-groups.html





